Increase Your Online Security with this Article
Covid compliance forced physical shops to close and accelerated the use of technology to make purchases and communicate. Increased tech use can mean users get lax with their password security and either re-use their passwords or create insecure passwords.
Organisations such as Evil Corp (see resources below) exploit thousands of individuals and companies with poor security worldwide yearly, and they’re getting away with it. Once perimeter defences have been breached, many hackers will move laterally through companies systems due to inferior network segmentation, gaining access to sensitive data.
Having seen relatives become victims of cybercrime and seeing senior staff in previous roles get duped into handing over their work passwords to fraudsters, it’s essential to educate everyone on the simple steps to keep their virtual (and operational) security at the top of their list.
It’s Okay. I’ve Got Site Lockdown and CAPTCHA.
Many users assume that a mixed security approach of minimum password requirements, password failure lockdowns, and CAPTCHA (Completely Automated Public Turing test to tell Computers and Humans Apart) diminish the threat against having their account hacked.
These techniques will help against brute force attacks (where a hacker will sequentially try thousands of password combinations starting at ‘a’ then moving onto ‘aa’, for instance), but more sophisticated attacks are now happening.
Email Spraying
While site lockdown and CAPTCHA will help slow down attacks (site lockdowns will limit the number of attempts to log into a system), criminals are now targeting passwords.
The NCSC has published a separate analysis of the 100,000 most commonly re-occurring passwords that third parties have accessed in global cyber breaches, and an independent study amongst businesses found:
Organisations that had accounts with passwords that featured in the top 1,000 passwords
Organisations that had accounts with passwords that featured in the top 10,000 passwords
75% of the participants’ organisations had accounts with passwords that featured in the top 1,000 passwords
87% had accounts with passwords that featured in the top 10,000
Below are five simple steps to help combat being a victim of cybercrime. They’re simple, quick and worth sharing with your business network and family:
1. Passwords and Passpack
To help combat the issue of having to remember many secure passwords across numerous platforms commercially, when I worked in Rippleffect, we rolled out the use of Passpack.
Passpack, which is a password manager, described itself as providing:
“…the tools that teams and individuals need to securely organise, collaborate and store your passwords with strong encryption and administrative controls”.
In a business, it’s helpful to have the ability to allow or remove access to stored passwords when people come and go – but from an individual point of view, having a password manager allows for much more secure passwords without having to remember them.
Using a password manager means you need a very secure password for the admin access – Passpack will also not allow you to recover your secondary passphrase. Forget it, and it’s gone.
Another password manager I’ve also used is OnePassword, though I found the user interface a little more confusing than Passpack.
Most browsers now also come with an indigenous password management system to save passwords for specific sites.
These systems do work well, though the more advanced tools of third-party password managers may appeal more to those who have more in-depth needs (such as additional fields). The third-party applications can also be easily accessed if you don’t have the browser you’ve saved all the passwords on, though be wary of accessing password managers on public computers (which may have a keylogger installed) and over unknown wifi.
2. Increase Your Password Security
Technically speaking, the longer and more complex passwords are, the harder they will be to guess. For instance, having a random 20 character password including letters, numbers, and special characters will be hard to crack. But realistically, as a human, you’re probably going not to remember it, and if you do, you’ll use it for more than one platform to log into.
Having the same password across multiple platforms is a sure-fire way to let hackers move laterally from a low-security forum to hacking something more critical.
To try and find a happy medium between the two, the NCSC suggests using a password made up of three words that you can easily remember for a given platform. You’ll still need to comply with the minimum password requirements for the site you’re logging into (e.g. one capital letter and a unique character), but the three words should increase the security of your data and allow you to remember it. Failing that, if you’ve got your password storage set up as above, it won’t matter too much if you forget.
3. Use At least 2 Factor Auth / MFA Auth
This is one of my favourite ways to help protect your logins. As it suggests, two-factor authentication requires a user to put in their primary details (e.g. username and password) and a second factor.
The second factor can come in several forms. The most common is an SMS message to your phone which most banks now use.
Interestingly, Amazon Web Services (AWS) have changed the name of 2-factor to multi-factor, and they’ve dropped the use of SMS to secure their servers presumably because SMS isn’t as secure as the alternatives from the likes of spoofing.
AWS Identity Access Management (IAM) has stepped up their security on this; you’ll get a warning to add it to the Root account (the primary account you started with, which has access to all areas).
The options other than SMS come in the form of authenticator apps such as TWILIO. Here you associate your account with TWILIO, which generates a code to add in as your second authentication method.
Having these on apps is excellent as it makes it just as accessible as using the SMS method.
Some systems also need the user to have a separate piece of hardware – similar to those banks used to use, e.g. a tamper-evident hardware key fob device. These are generally used by higher security institutions such as enterprise-scale businesses and the government and have a more significant cost attached to their use.
The NCSC’s advice on MFA? “we strongly recommend that everyone switches it on for their email (if possible) and any other online service they care about.”
4. Have I Been Pwned (HIBP)
Head over to the HIBP website. Here Troy Hunt, who works for Microsoft (see the plug to Azure), has created a website that will help you see if your data has been taken from any breaches.
It’s an excellent first step to start securing your details, though there are plenty of caveats about how to use the information you get from it and its accuracy.
Take a look at the FAQ’s and if you feel it’s valuable, sign-up. It’s free, and the link is in the resources below.
5. Password List Check
So the first three points on this list are how to help secure your passwords and data. The fourth is a stepping stone to start checking where your data may have been released into the wild.
This last step is an absolute must to bolster your security profile.
As mentioned above, the NCSC has published this list of 100,000 most common passwords.
Use the password link here to see the passwords https://bit.ly/3eNbtQo.
After searching for your passwords (then looking up naughty words), you’ll notice that many of these passwords are pretty ‘secure’ in conventional terms, including the number of characters used and adding a “salt” to the password.
Because they have been used so much, hackers can bypass the usual need for brute force and concentrate on these; it’s especially worrying as users who do have a secure looking password may not have turned on Multi-Factor authentication because they think their password fits all the minimum security checks and is secure.
Conclusion and Summary
No way of working or system will be 100% foolproof to stop hackers; indeed, many items of site security are entirely out of your hands – which is why having secure passwords and limiting cross-platform password use is essential.
Using the steps below, though, should help decrease the probability of either a direct compromise to your account or in the event of a sitewide security incident.
- Make sure your passwords aren’t on the list – if they are, change them.
- Check the Have I Been Owned Link and act on the feedback.
- Ensure all apps and websites which have multi-factor authentication have it
- Check through your synced passwords on Chrome or Safari to see how strong they are, and there are no duplicates.
- Use a system like Passpack or 1 One Password to store hard to remember passwords (but make sure access to these systems has a strong password)!
Next steps? Share this article and shout about security with friends and family. If you’re interested in the details, check out the resources below for more information.
Security Article Resources
Pact Coffee Voucher Codes
Looking for a Pact Coffee Voucher code? Here are a few I can recommend. It makes a great change; it’s tastes really good and comes in a load of different grinds and flavours. My favourite is probably the Bourbon Cream Espresso – but use the code to explore all the flavours Pact Coffee has to offer! Use the voucher code “PACTPERK” to get your discount now.
Like the Above? Below Are Hands Down the Best Blog Articles You’ve Ever Read
A Drive to Remember
A Drive to Remember: My TVR Adventure Across Europe If someone had told me a year ago, "Would you fancy [...]
Security Security Security
Increase Your Online Security with this Article Covid compliance forced physical shops to close and accelerated the use of [...]
Going Quantum
How to Use Amazons Quantum Computers If annealing, superposition, and qubits all sound like new Netflix films to [...]
Digital Currency: The Next Fintech Challenge?
With the likes of Dorthy Perkins and Topshop on the brink of collapse, what can governments do to stimulate spending [...]
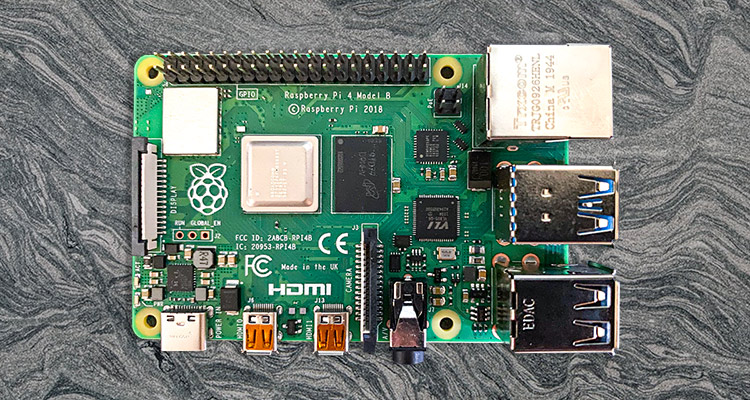
Raspberry Pi Hedgehog Camera
Raspberry Pi Hedgehog Camera Lockdown 1.0 was a golden opportunity to learn some new skills, move out of [...]
Making Meetings More Manageable
"Never ask a question you didn't know the answer too". The first rule I was taught in advocacy at law school. [...]
5 Tips for Setting up Remote Agile Teams
During the recent Maxwell Bond Webinar (kindly organised by Riana Butler) on "Agile Project Delivery" I sat as a panellist. There [...]
Don’t Test The Testers
In the last 20 years of delivery I've lost count of the number of times I've heard "No, we don't need [...]
The Grand Bore
The room erupted in laughter when my colleague accidentally had a double typo in a sprint meeting and wrote “twat” instead [...]
Using Clouds to Help the Homeless
The tech ops guys were banging on about CloudFlare again, and I had no idea why. Did Cloudflare sponsor them? Surely it [...]
Digital Disappointment
Frustration increased as my colleague prodded her greasy index finger on my Macbook Pro’s screen and tried to swipe the web [...]
When Zero Talent Counts
Getting a highly qualified candidate with the most in-depth knowledge about your company’s chosen technology is the most valuable potential employee [...]
Grammarly and Linkedin, a Perfect Partnership?
This weekend I was told by a beautiful girl in a library how to bring my “A” game when writing Linkedin [...]
Do Project Managers Need KPIs
Key Performance Indicators, they’re not something a project manager needs to worry about right? They’re just a buzzy term used by [...]
Getting Team Buy In
What's the best way to get the most out of your team? Rule them with an iron fist and push them [...]
Delphix fixes Data Gravity
The internet is rapidly growing, and it's becoming more and more commonplace just to accept that every site you use pulls [...]
Maffins Wager
The accepted three pillars of project management are: On time, to budget and the right standard. Assuming the latter two are [...]
Failure is not an option fallacy
Many managers use the term "failure is not an option". One of the best pieces of advice I've ever heard came [...]
Context Switching in Programming
Ben Maffin People often talk about how interruptions disrupt their flow and the ability to produce good quality, consistent [...]
The XOX Method for Project Success
A common mistake made by project owners is to create a system which is either over engineered or is overly feature [...]
Live in 2 Days The MVP Conjecture
Getting a site up and running can take months or years for some companies. Can you do this quicker? What are [...]
What’s The Point to Pair Programming
Pair programming is a technique which essentially puts at least two developers on any given project at any time. So What's The [...]
Technical Debt, What is It
Technical debt is often an overlooked element of development but has far reaching implications on profit, delivery and quality of a project. What [...]
What Is Project Success
Like many questions in digital project management, this is a trickier to answer than most people initially think You'll find numerous answers, [...]

























Leave A Comment